In November, the Open Technology Fund announced its new organizational status as an independent non-profit corporation, becoming the first-ever USAGM grantee dedicated to protecting human rights by combating online censorship and advancing Internet freedom worldwide. Also this month, OTF hosted its annual Summit, bringing together a subset of OTF’s actively supported projects, fellows, and service providers for a two-day event that encourages new connections and instigates new collaborations among the Internet freedom community. The OTF team also continued reviewing and responding to the more than 200 concept notes received during the November 1 round, while also accepting applications for the upcoming January 1 round.
Notable accomplishments
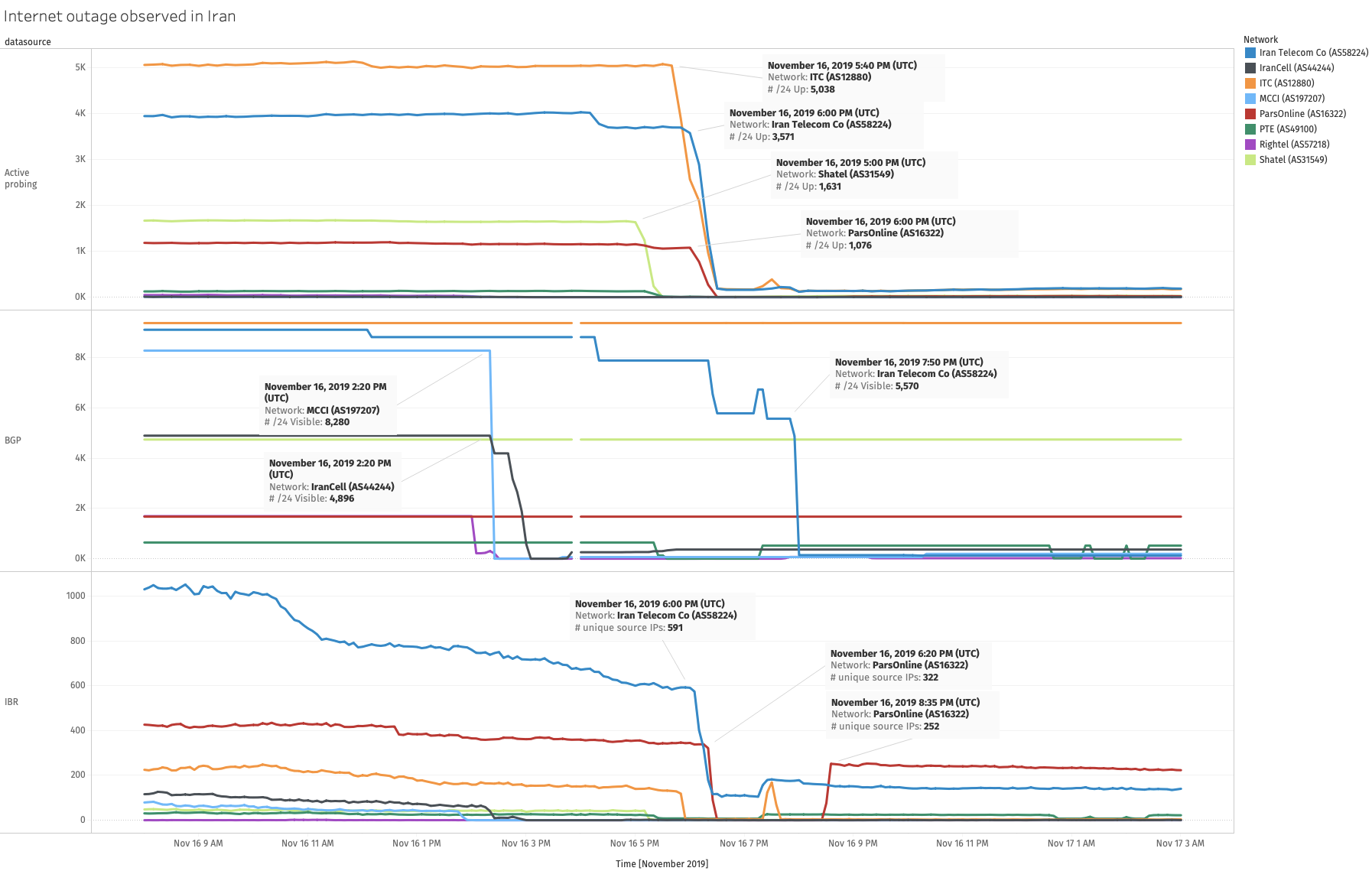
- In collaboration with CAIDA/IODA, the Open Observatory of Network Interference (OONI) released a report on Iran’s recent Internet shutdown, compiling technical measurement data demonstrating the breadth and scale of a largescale communications blackout imposed by the government in the wake of widespread protests. The report shows network-by-network how the global Internet was switched off and made completely inaccessible for several days for nearly all Iranians, with citizens only able to access the country’s national intranet. The below chart, compiled with IODA data, shows when service for each network operator in Iran was cut off:
- Certbot version 1.0 was released, the first non-beta version for the tool that makes it easier for websites to adopt HTTPS encryption through the automated deployment of Let’s Encrypt certificates. To date, more than two million website administrators are using Certbot to encrypt their site traffic and help protect website visitors. Learn more and access the tool here.
- Through an OTF-supported effort on behalf of the DG7 partners, Deutsche Welle joined the coalition of international broadcasters offering a dedicated .onion address for their website – a censorship-resistant mirror site that is only accessible via the Tor browser, allowing people in countries where their website is blocked to access the site’s news and information. The BBC and RFA have also launched their .onion sites, with sites for RFE/RL and VOA forthcoming.
- In its first year of existence, the App Store Censorship project has identified over 2,500 apps which have been censored in the China App Store alone. Other top app stores with sizable takedowns included Hong Kong (214), Saudi Arabia (197), Indonesia (179), Hungary (178), and United Arab Emirates (176). Data and information gathered via the platform is freely accessible to journalists, activists, policymakers, and everyday citizens. You can explore the App Store Censorship tool here, or follow the project @applecensorship, where App Store changes are automatically detected and tweeted. The project is also undergoing volunteer-driven translation into multiple languages via Localization Lab; contribute here.
- Several new projects are now receiving OTF support, including:
- Relaynet, a project focused on building networked apps that can remain connected in the event of a complete Internet shutdown. Relaynet-compatible apps can be centralized or decentralized, and pre-existing software can also be adapted to use the technology (Relaynet’s proof of concept made it possible to use Twitter, for example). With OTF’s support, Relaynet will build the foundation of the technology so it can be used by desktop and Android apps.
- Geneva, a project that seeks to use artificial intelligence to automatically learn how to circumvent in-network censorship. Testing the tool in China, India and Kazakhstan, Geneva “…found dozens of ways to circumvent censorship by exploiting gaps in censors’ logic and finding bugs that the researchers say would have been virtually impossible for humans to find manually.” The project, incubated at the University of Maryland’s Breakerspace research lab, was recently presented in a paper (pdf) at the 2019 Association for Computing Machinery (ACM) Conference on Computer and Communications Security (CCS). You can read more about the project in this Boing Boing article.
- Azerbaijan Internet Watch, a project that will address the large information gap that currently exists around critical developments related to Internet freedom in Azerbaijan. In the absence of open political discussions offline in the country, these conversations have increasingly moved to social media platforms, especially Facebook, YouTube and Instagram. Realizing this shift, authorities in Azerbaijan have already started exercising various forms of control mechanisms, from hacking Facebook pages that belong to popular political figures and parties, to blocking websites, issuing take down requests, spear phishing attempts and DDoS attacks against independent and opposition media platforms. Azerbaijan Internet Watch, or Az-NetWatch for short, will map online censorship and surveillance in the country through monitoring, documenting and reporting on deployed information controls.
- PiGuard, a project that will develop and deploy censorship-resistant WireGuard-based VPN connection services for independent media and human rights organizations. VPNs are routinely used by activists, bloggers, and journalists to secure online communication and circumvent censorship. However, they are quite easy to shut down just by blocking the IP address of the server providing the VPN service. Utilizing WireGuard’s “IP Roaming” feature, which allows a device to automatically connect to a new VPN server in case the previous server got blocked, this project seeks to embed WireGuard in small and inexpensive servers to create a WiFi hotspot, allowing the connected organizations to operate more safely and overcome censorship.
- The Community Lab provided support for the second annual Bread & Net unconference, held November 15-17 in Beirut, Lebanon. The participant-driven gathering brought together stakeholders from across the Middle East and North Africa (MENA) region to strengthen efforts to advance human rights in digitally networked spaces. Topics covered included Internet shutdowns in the Arab region, attacks to free expression online, and digital security education. You can read a recap of the event here.

